Koom Ransomware is the Another Member of the STOP/Djvu Ransomware Family
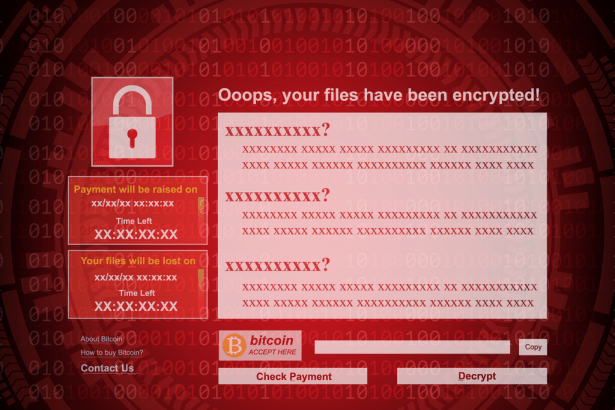
Since its discovery in 2018, the STOP/Djvu ransomware family has released hundreds of new variants as it quickly became one of the world’s most prolific ransomware groups. Koom Ransomware was uncovered by researchers as yet another strain. It is referred to as Koom based on the .koom extension it uses to append infected files. The ransomware operates like its counterparts in the STOP/Djvu family and encrypts files before making a ransom demand.
Koom Ransomware scans a victim’s PC to look for user-generated files. It then targets files that may contain valuable information, including databases, spreadsheets, archives, pictures, and videos. Additionally, the hackers behind Koom Ransomware deliver a ransom note named “_readme.txt,” which contains information regarding the ransomware and the hackers’ ransom demands.
The Ransom Demand Associated with Hoop Ransomware
Koom Ransomware’s operators promise a decryption key to unlock the affected files in exchange for $980. However, they do offer a 50% discount if victims establish communication within 72 hours after encryption. The ransom note also instructs users to contact the criminals via the emails helpmanager@mail.ch or restoremanager@airmail.cc. Like most ransomware operators, the Koom Ransomware owners offer to decrypt one file for free to display their ability to unlock all the affected files should the victim pay up.
Although cooperating with hackers seems like an easy way out of the situation, we strongly advise viewers not to engage the hackers and employ a reputable malware remediation program to scan for and rid their system of the destructive Koom Ransomware.To prevent data loss in the case of another ransomware attack in the future, please consider backing up your data on an external hard drive or virtual cloud storage.