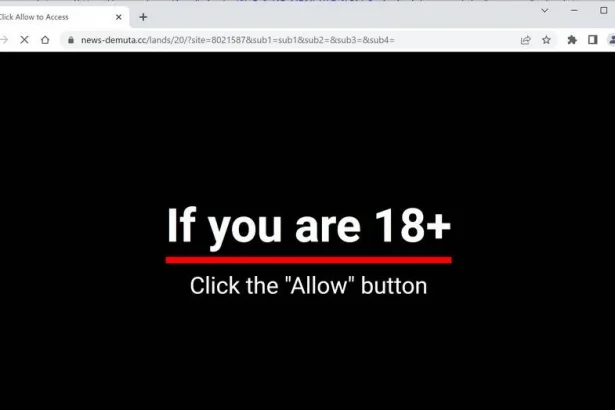
In the digital age, where our lives are intertwined with the internet, cyber threats continue to evolve, posing risks to our security and privacy. One such threat that has garnered attention is the “If You Are 18+ Tap Allow” malware. This deceptive entity lurks in the shadows of the web, masquerading as innocuous content while stealthily compromising users’ devices. In this comprehensive guide, we delve into the intricacies of this cyber menace, its modus operandi, detection methods, and most importantly, how to eradicate it from your system and prevent future infections.
Understanding the Threat
The “If You Are 18+ Tap Allow” malware operates as a browser hijacker, infiltrating users’ browsers through deceptive tactics. It often presents itself as a pop-up message, enticing users to click on the “Allow” button, purportedly to access adult content. However, this seemingly innocuous action initiates a cascade of undesirable consequences.
Once granted permission, this malware wreaks havoc on users’ browsing experiences. It hijacks search engines, alters homepage settings, inundates users with intrusive advertisements, and tracks their online activities. Furthermore, it exposes users to potential scams, malvertising, and phishing schemes, putting their sensitive information at risk.
Identifying the “If You Are 18+ Tap Allow” malware can be challenging, as it operates under various aliases and disguises. Some detection names for this malware include browser hijacker, adware, or potentially unwanted program (PUP). Similar threats include other browser hijackers like “Your Browser Has Been Locked,” “Congratulations, You’ve Won,” and “Your Computer is Infected” pop-ups.
Removal Guide
- Access Browser Settings: Navigate to your browser’s settings menu.
- Manage Notifications: Locate the section for notifications or permissions.
- Revoke Permission: Find the entry related to “If You Are 18+ Tap Allow” and revoke its permission to display notifications.
- Clear Browser Data: Remove cookies, cache, and browsing history to eliminate any remnants of the malware.
- Reset Browser Settings: Consider resetting your browser to its default settings to ensure complete removal.
Best Practices for Prevention
- Exercise Caution: Be wary of suspicious websites and avoid clicking on enticing pop-ups or ads.
- Stay Updated: Keep your operating system, browser, and security software up to date to patch any vulnerabilities.
- Install Ad Blockers: Consider using ad-blocking extensions or software to mitigate the risk of encountering malicious ads.
- Educate Yourself: Stay informed about common cyber threats and phishing tactics to recognize and avoid potential dangers.
- Use Security Software: Invest in reputable antivirus or antimalware software to provide an additional layer of protection against emerging threats.
By following these proactive measures and remaining vigilant while browsing the internet, you can safeguard yourself against the “If You Are 18+ Tap Allow” malware and other similar cyber threats, preserving your online security and privacy.