Overview of the Threat
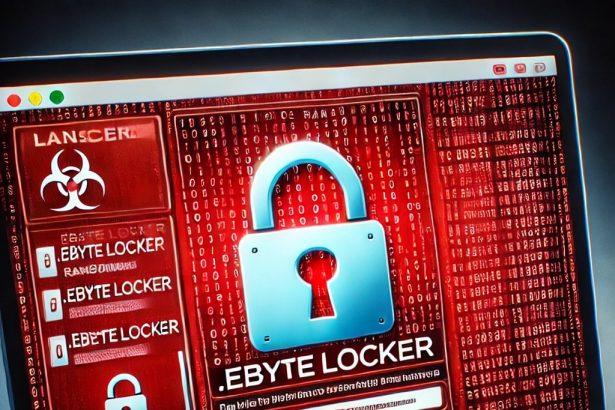
EByte Locker is a ransomware variant based on the Prince ransomware family. It encrypts files on an infected system, appends the “.EByteLocker” extension to them, and delivers a ransom note titled “Decryption Instructions.txt.” Victims are instructed to pay a ransom in cryptocurrency to recover their files. This malware poses a severe risk to data integrity and user privacy.
Summary of EByte Locker Threat
| Category | Details |
|---|---|
| Threat Type | Ransomware, Crypto Virus, Files Locker |
| Encrypted File Extension | .EByteLocker |
| Ransom Note File Name | Decryption Instructions.txt |
| Associated Email | example@airmail.cc |
| Detection Names | Avast (Win64:Malware-gen), Combo Cleaner (Generic.Ransom.Prince.A.F6533D94), ESET-NOD32 (A Variant Of WinGo/Filecoder.HG), Kaspersky (HEUR:Trojan-Ransom.Win64.Generic), Microsoft (Ransom:Win64/PrinceRansom.YAA!MTB) |
| Symptoms | Files encrypted with a new “.EByteLocker” extension, desktop wallpaper changed, ransom note displayed, inability to open previously functional files |
| Damage | Data encryption, possible additional malware infections, potential password theft |
| Distribution Methods | Malicious email attachments, infected downloads, compromised websites, malicious ads, exploit kits, USB devices |
| Danger Level | Severe |
Download SpyHunter Now & Scan Your Computer For Free!
Remove this and any other malicious threats to your system by scanning your computer with SpyHunter now! It’s FREE!
Detailed Threat Description
EByte Locker ransomware encrypts files on a victim’s computer, rendering them inaccessible. Encrypted files are renamed with the ".EByteLocker" extension, such as example.jpg becoming example.jpg.EByteLocker. The ransomware alters the desktop wallpaper and creates a ransom note named "Decryption Instructions.txt."
The ransom note warns victims not to modify or rename the encrypted files, as this could make decryption impossible. Victims are instructed to contact the attackers via the provided email address (example@airmail.cc) and make a payment in cryptocurrency. However, paying the ransom is highly discouraged because it does not guarantee the recovery of the encrypted files.
How EByte Locker Infects Systems
EByte Locker typically infiltrates systems through the following methods:
- Malicious Email Attachments: Users may receive emails containing malicious links or attachments (e.g., MS Office documents with macros or executable files).
- Compromised Websites and Ads: Visiting infected websites or interacting with malicious ads can trigger the download of ransomware.
- Pirated Software and Cracks: Downloading software from unreliable sources, especially torrents, increases the risk of malware infection.
- USB Devices and External Storage: Infected drives can spread the ransomware to new systems.
- Exploited Vulnerabilities: Cybercriminals leverage unpatched software vulnerabilities to inject malware into devices.
Consequences of Infection
- Data Encryption: All files are locked with strong encryption, making them inaccessible without a decryption key.
- Potential Data Loss: If victims do not have a backup and decryption tools are unavailable, files may be permanently lost.
- Spread Across Networks: The ransomware can propagate through local networks and encrypt files on connected systems.
- Additional Malware: EByte Locker may install other malicious programs, such as password stealers and spyware, further compromising security.
How to Remove EByte Locker Ransomware
/
Step 1: Disconnect from the Internet
To prevent further encryption or propagation, immediately disconnect your system from the internet.
Step 2: Boot in Safe Mode
- Restart your computer.
- While it’s booting, press the appropriate key (e.g., F8) to access the boot menu.
- Select Safe Mode with Networking.
Step 3: Use SpyHunter to Eliminate the Malware
SpyHunter is a powerful anti-malware tool designed to detect and remove ransomware like EByte Locker. Follow these steps:
- Download SpyHunter from its official website using a clean device.
- Transfer the setup file to the infected system via a USB drive.
- Install SpyHunter and run a full system scan.
- Once the scan is complete, remove all detected threats.
Step 4: Restore Encrypted Files
If a backup exists, restore your files after removing the ransomware. If no backup is available, check for legitimate third-party decryption tools online. Avoid using tools from unknown or untrustworthy sources, as they may contain malware.
Preventive Measures Against Ransomware
- Regular Backups: Maintain secure backups of critical data on external drives or cloud storage.
- Update Software: Install updates and security patches for your operating system and software regularly.
- Use Antivirus Software: Ensure you have reliable antivirus software installed and keep it up to date.
- Avoid Suspicious Emails: Do not open email attachments or click on links from unknown sources.
- Use Strong Passwords: Secure your accounts with strong, unique passwords and enable multi-factor authentication (MFA) where possible.
- Disable Macros: Configure MS Office to block macros from untrusted sources.
- Secure Network Settings: Use firewalls and avoid connecting to unsecured Wi-Fi networks.
- Educate Users: Train employees and family members on recognizing phishing attempts and safe browsing practices.
Conclusion
EByte Locker ransomware is a dangerous threat that encrypts valuable files and demands payment for their recovery. While the encryption process often renders files inaccessible, taking proactive measures—such as using SpyHunter to remove the malware—and enforcing preventive practices can help mitigate the risks of ransomware attacks. Always maintain backups and stay vigilant to safeguard your data from cybercriminals.
Download SpyHunter Now & Scan Your Computer For Free!
Remove this and any other malicious threats to your system by scanning your computer with SpyHunter now! It's FREE!