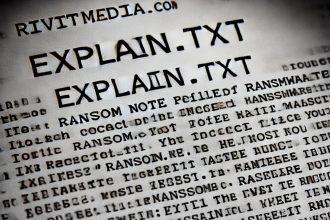
innok Ransomware: Everything You Need to Know and How to Remove It
Cybersecurity experts have identified innok ransomware as a significant threat. Closely resembling the BlackPanther ransomware, innok encrypts files, appends the…
Cash-searcher[.]com: A Deceptive Website to Avoid
In the ever-evolving landscape of online threats, deceptive websites like cash-searchercom aim to exploit unsuspecting users. Cash-searchercom presents itself as…
Baraag.net and How to Protect Yourself
Baraag.net is a microblogging platform within the Mastodon network, widely known for hosting explicit anime-style artwork, including hentai and furry…
Clearnview Pop-up – Should You Be Worried?
The Clearnview.com pop-up issue has been raising concerns among users worldwide. This problem stems from suspicious activity linked to browser…
Behque[.]click
Rogue websites like behqueclick pose significant threats to users by leveraging deceptive tactics to deliver harmful ads, scams, and even…
Euopue[.]click: A Dangerous Push Notification Scam
Euopueclick is a malicious website designed to deceive users into granting permission to display intrusive notifications. This page utilizes various…
How to Remove Flightsettle[.]site Notifications and Avoid Related Threats?
Flightsettlesite is a deceptive website that uses clickbait tactics to gain permission to display notifications. These notifications often lead to…
EByte Locker Ransomware: Detailed Analysis and Removal Guide
Overview of the Threat EByte Locker is a ransomware variant based on the Prince ransomware family. It encrypts files on…
Traw Dapp Removal
Traw Dapp is a potentially unwanted application (PUA) identified by security vendors as malicious. Despite lacking clear functionality, this application…
Spring Ransomware: A Dangerous CONTI-Based Threat You Need to Know
Spring ransomware is a malicious program stemming from the notorious CONTI ransomware family. It encrypts user files, appending a unique…