Mastering Your Antimalware Control Panel: A Step-by-Step Guide to Optimal Security
You’re browsing the internet, clicking through emails, and downloading files, completely unaware that lurking in the shadows is malware waiting…
Mastering Your Antimalware Control Panel: The Ultimate Guide to Keeping Your System Secure
Think your antivirus software is doing all the heavy lifting for you? Think again. While having a solid antimalware tool…
The Best Antimalware Control Panels: Top Solutions for Cybersecurity Management
Imagine waking up one morning, checking your emails, and realizing your business has been hit by a devastating malware attack…
Mastering Your Anti-Malware Control Panel: The Features That Keep You Safe
Imagine this: You install an anti-malware program to protect your device, but when you open it, you're hit with a…
Affordable EDR for SMBs: Protect Your Business Without Breaking the Bank
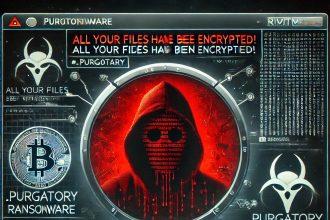
Imagine this: You’re running your small business, focusing on growth and customer service, when suddenly, your systems lock up. A…
SMB Security Software: Protect Your Business from Cyber Threats
Imagine waking up to find your business locked out of its systems, held hostage by ransomware. Or worse, discovering that…
The Essential Cybersecurity Toolkit for SMBs: Must-Have Solutions to Stay Secure
Imagine waking up to find that your entire business has been locked out of its systems, customer data stolen, and…
Mental Mentor: A Potentially Unwanted Application (PUA) Posing Privacy Risks
Mental Mentor is promoted as a self-improvement tool, offering dream interpretation, divination, and related courses. However, the software raises significant…
EpiStart (EpiBrowser) Removal Guide: Protect Your System from This Rogue Browser
Understanding the EpiStart (EpiBrowser) Threat EpiStart, also known as EpiBrowser, is a rogue browser based on the open-source Chromium project.…
TorNet Malware: A Lurking Backdoor Threat and How to Eliminate It
TorNet is a dangerous backdoor malware that stealthily infiltrates systems, enabling cybercriminals to gain unauthorized access and deploy additional malicious…